Identify gutter oil and try these tricks.
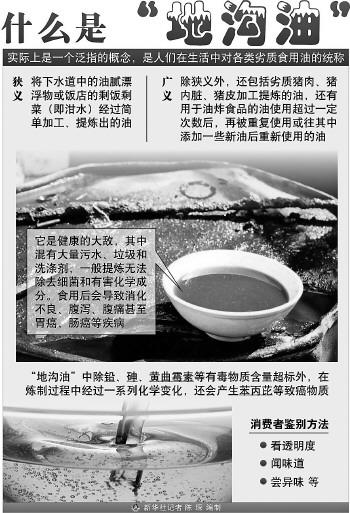
So, is there a simple way to identify gutter oil? We might as well listen to what food science experts and insiders say.
one
There is no good way to scientifically identify waste oil at present.
In an era of paying attention to food safety, the ideal state is that when you go to a restaurant, you take out a test paper and dip it in the dish. After a while, you take it out and compare it with the spectrum table, and then shout, "Boss, change the oil!"
However, the reality is that up to now, scientists have not found an ideal means to detect and identify gutter oil.
"Oil mixed with oil, fairy sorrow, fairy is difficult to separate it. Waste cooking oil has a history of more than 20 years. Even today, we can still see waste cooking oil in rural markets and urban-rural junction markets, and we also feel that it has entered the dining hall. If calculated by tonnage, there should be millions of tons of waste oil digested every year. I am very embarrassed. We can’t find a very effective technical means to identify it. This oil is gutter oil, and this oil is not gutter oil. " When attending a CCTV program, Hu Xiaosong, vice president of the College of Food Science and Nutritional Engineering of China Agricultural University, once said this.
Hu Xiaosong pointed out that the current detection methods have not overcome this technology and cannot scientifically distinguish the quality of oil, but the Ministry of Science and Technology has set up a special project for this matter, and I believe that it will be possible to distinguish the quality of oil by scientific means in the near future.
2
Traditional detection methods have certain limitations.
In the view of scientific researchers, the difficulty in treating gutter oil lies in that it is difficult to distinguish gutter oil from ordinary oil only from appearance and sense after refining processes such as washing, distillation, decoloration and deodorization. Illegal traders will also mix waste oil into edible oil, and if the content is small, it is even more difficult to detect.
He Dongping, a professor at the School of Food Science and Engineering of Wuhan Institute of Technology, has been engaged in the research of gutter oil for many years. In He Dongping’s view, the traditional detection methods only grasp a certain characteristic of gutter oil, and no method can effectively detect gutter oil from different sources at the same time, which sometimes leads to a large detection error and more possibility of misjudgment.
Wang Le, a graduate student of Wuhan Institute of Technology, once developed a blue test paper. With the increasing proportion of waste oil, the blue test paper will show yellow-green, light yellow and bright yellow. This is based on the "accumulation" of oil to detect the purity of oil, but this method is also limited by the proportion of waste oil added.
On the Internet, you can find a company specializing in the production of "Quick Detection Kit for Waste Oil", but from the instructions provided by the company, "for some unpurified oils (such as sesame oil, pepper oil, etc.) and oils with other ingredients (such as Chili oil), this method is easy to produce false positives".
three
Identify the waste oil refrigerator?
Senior chef Feng Peng, who once worked as a chef and executive in many big restaurants in Beijing, said that under normal circumstances, gutter oil and ordinary oil can’t be distinguished, and it is inevitable to be fooled when purchasing. He can only judge by practice: restaurants usually need to oil before cooking. In this "lubricating oil" process, good oil can be used seven or eight times repeatedly, while waste oil will become sticky and have a spicy taste after being used for up to three times.
"In addition, when the outdoor temperature is low, waste oil will solidify like palm oil, so people often use waste oil to pretend to be palm oil." Feng Peng said that gutter oil can be identified in winter and can be tested in the refrigerator in summer. Some media think that gutter oil has a taste and can be smelled out. In addition, it contains a lot of water, and the pot will explode. Feng Peng thinks these are nonsense, because water can’t be mixed into oil at all, and gutter oil has no odor.
four
How should we identify waste oil?
Take a look. Look at the transparency, pure vegetable oil is transparent, and the transparency will decrease due to the mixing of alkali grease, wax and impurities in the production process; Look at the color, pure oil is colorless, and the oil will be colored because the pigment in the oil is dissolved in the oil in the production process; Look at the sediment, its main component is impurities.
Second smell. Each oil has its own unique smell. You can drop a drop or two of oil on your palm, rub your hands together, and smell it carefully when you are hot. Oil with odor indicates that there is a problem with the quality, and it is likely to be waste oil with odor; If there is a smell of mineral oil, you can’t buy it.
Three tastes. Take a drop of oil with chopsticks and taste it carefully. The oil with sour taste is unqualified, the oil with bitter taste has been rancid, and the oil with peculiar smell may be waste oil.
Listen. Take one or two drops of oil from the bottom of the oil layer, coat it on flammable paper, light it and listen to its sound. The products with normal combustion and no noise are qualified products; If the combustion is abnormal and makes a "squeaky" sound, the water content exceeds the standard and it is an unqualified product; The "crack" explosion during combustion indicates that the water content of the oil is seriously exceeding the standard, and it may be adulterated products, so it is absolutely impossible to buy.
Five questions. Ask the merchant about the purchase channel, ask for the purchase invoice or check the sampling test report of the local food hygiene supervision department if necessary. (Comprehensive by this newspaper)